Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3
values | title stringlengths 1 994 | labels stringlengths 4 719 | body stringlengths 1 261k | index stringclasses 13
values | text_combine stringlengths 95 261k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
71,620 | 15,207,809,833 | IssuesEvent | 2021-02-17 01:04:18 | billmcchesney1/foxtrot | https://api.github.com/repos/billmcchesney1/foxtrot | closed | CVE-2020-27216 (Medium) detected in jetty-webapp-9.4.11.v20180605.jar, jetty-webapp-9.4.18.v20190429.jar - autoclosed | security vulnerability | ## CVE-2020-27216 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jetty-webapp-9.4.11.v20180605.jar</b>, <b>jetty-webapp-9.4.18.v20190429.jar</b></p></summary>
<p>
<details><summar... | True | CVE-2020-27216 (Medium) detected in jetty-webapp-9.4.11.v20180605.jar, jetty-webapp-9.4.18.v20190429.jar - autoclosed - ## CVE-2020-27216 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries ... | secu | cve medium detected in jetty webapp jar jetty webapp jar autoclosed cve medium severity vulnerability vulnerable libraries jetty webapp jar jetty webapp jar jetty webapp jar jetty web application support library home page a href ... | 1 |
433,470 | 30,330,157,763 | IssuesEvent | 2023-07-11 05:31:20 | aws/karpenter | https://api.github.com/repos/aws/karpenter | opened | Improve the capacity dashboard | documentation | ### Description
**How can the docs be improved?**
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" ... | 1.0 | Improve the capacity dashboard - ### Description
**How can the docs be improved?**
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Plea... | non_secu | improve the capacity dashboard description how can the docs be improved please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do... | 0 |
304,649 | 26,293,905,813 | IssuesEvent | 2023-01-08 18:52:53 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix metrics.test_tensorflow_log_cosh | TensorFlow Frontend Sub Task Failing Test | | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/3865845421/jobs/6589592684" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_me... | 1.0 | Fix metrics.test_tensorflow_log_cosh - | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/3865845421/jobs/6589592684" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>FAILED ivy_tests/test_ivy... | non_secu | fix metrics test tensorflow log cosh jax img src failed ivy tests test ivy test frontends test tensorflow test metrics py test tensorflow log cosh e assertionerror e falsifying example te... | 0 |
36,832 | 15,082,198,737 | IssuesEvent | 2021-02-05 14:16:08 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | aws_launch_template does not support instance_types even though aws_eks_node_groups does | enhancement service/ec2 service/eks | <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not l... | 2.0 | aws_launch_template does not support instance_types even though aws_eks_node_groups does - <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the orig... | non_secu | aws launch template does not support instance types even though aws eks node groups does community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or other comments that do not add relevant ... | 0 |
148,936 | 19,560,740,935 | IssuesEvent | 2022-01-03 15:53:36 | shaimael/Webgoat | https://api.github.com/repos/shaimael/Webgoat | opened | CVE-2018-20676 (Medium) detected in bootstrap-3.1.1.min.js | security vulnerability | ## CVE-2018-20676 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile f... | True | CVE-2018-20676 (Medium) detected in bootstrap-3.1.1.min.js - ## CVE-2018-20676 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most po... | secu | cve medium detected in bootstrap min js cve medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library webgoat l... | 1 |
91,532 | 15,856,498,881 | IssuesEvent | 2021-04-08 02:29:04 | AlexRogalskiy/electron-vue-template | https://api.github.com/repos/AlexRogalskiy/electron-vue-template | opened | CVE-2020-28498 (Medium) detected in elliptic-6.5.2.tgz | security vulnerability | ## CVE-2020-28498 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.or... | True | CVE-2020-28498 (Medium) detected in elliptic-6.5.2.tgz - ## CVE-2020-28498 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>... | secu | cve medium detected in elliptic tgz cve medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file electron vue template package json path to vulnerable library electron vue template node modules ell... | 1 |
60,530 | 6,700,903,985 | IssuesEvent | 2017-10-11 07:34:38 | owncloud/client | https://api.github.com/repos/owncloud/client | closed | Triggering log in should re-ask about previously rejected certificates | Enhancement ReadyToTest | Suggested by @SamuAlfageme in https://github.com/owncloud/client/issues/5728#issuecomment-305225953:
Currently rejecting a certificate is permanent for the duration the client is running. So the client will never ask about a certificate again if it was rejected once unless the client is restarted.
What if the cl... | 1.0 | Triggering log in should re-ask about previously rejected certificates - Suggested by @SamuAlfageme in https://github.com/owncloud/client/issues/5728#issuecomment-305225953:
Currently rejecting a certificate is permanent for the duration the client is running. So the client will never ask about a certificate again ... | non_secu | triggering log in should re ask about previously rejected certificates suggested by samualfageme in currently rejecting a certificate is permanent for the duration the client is running so the client will never ask about a certificate again if it was rejected once unless the client is restarted what if th... | 0 |
212,651 | 23,934,095,844 | IssuesEvent | 2022-09-11 01:02:14 | brightcove/cloud-custodian | https://api.github.com/repos/brightcove/cloud-custodian | closed | CVE-2022-21698 (High) detected in multiple libraries - autoclosed | security vulnerability | ## CVE-2022-21698 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>github.com/docker/docker-v20.10.12</b>, <b>github.com/containerd/containerd-v1.5.11</b>, <b>github.com/docker/distrib... | True | CVE-2022-21698 (High) detected in multiple libraries - autoclosed - ## CVE-2022-21698 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>github.com/docker/docker-v20.10.12</b>, <b>github... | secu | cve high detected in multiple libraries autoclosed cve high severity vulnerability vulnerable libraries github com docker docker github com containerd containerd github com docker distribution github com docker docker moby project a collaborative p... | 1 |
480,528 | 13,853,488,382 | IssuesEvent | 2020-10-15 08:12:33 | geosolutions-it/MapStore2 | https://api.github.com/repos/geosolutions-it/MapStore2 | closed | Advanced settings problem for WMS and CSW services | Accepted Good first issue Internal Priority: High bug | ## Description
<!-- Add here a few sentences describing the bug. -->
It is no longer possible to click on the `Search on service selection` and `Enable localized styles` options from the Advanced Settings for a WMS service and it is no longer possible to click on the `Search on service selection` option for a CSW ser... | 1.0 | Advanced settings problem for WMS and CSW services - ## Description
<!-- Add here a few sentences describing the bug. -->
It is no longer possible to click on the `Search on service selection` and `Enable localized styles` options from the Advanced Settings for a WMS service and it is no longer possible to click on t... | non_secu | advanced settings problem for wms and csw services description it is no longer possible to click on the search on service selection and enable localized styles options from the advanced settings for a wms service and it is no longer possible to click on the search on service selection option for a csw se... | 0 |
191,571 | 22,215,807,677 | IssuesEvent | 2022-06-08 01:25:42 | ShaikUsaf/linux-3.0.35 | https://api.github.com/repos/ShaikUsaf/linux-3.0.35 | opened | CVE-2017-9077 (High) detected in linux-stable-rtv3.8.6 | security vulnerability | ## CVE-2017-9077 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page:... | True | CVE-2017-9077 (High) detected in linux-stable-rtv3.8.6 - ## CVE-2017-9077 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwrigh... | secu | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in base branch master vulnerable source files net dccp c ... | 1 |
132,625 | 18,268,801,087 | IssuesEvent | 2021-10-04 11:39:03 | artsking/linux-3.0.35 | https://api.github.com/repos/artsking/linux-3.0.35 | opened | CVE-2012-3510 (Medium) detected in linux-stable-rtv3.8.6, linux-stable-rtv3.8.6 | security vulnerability | ## CVE-2012-3510 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-stable-rtv3.8.6</b>, <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summar... | True | CVE-2012-3510 (Medium) detected in linux-stable-rtv3.8.6, linux-stable-rtv3.8.6 - ## CVE-2012-3510 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-stable-rtv3.8.6</b>, <b>linu... | secu | cve medium detected in linux stable linux stable cve medium severity vulnerability vulnerable libraries linux stable linux stable vulnerability details use after free vulnerability in the xacct add tsk function in kernel tsacct c in the linux... | 1 |
42,648 | 2,872,821,340 | IssuesEvent | 2015-06-08 14:09:41 | cultibox/cultibox | https://api.github.com/repos/cultibox/cultibox | closed | [culti] ecran principal : affichagesymbol lune | Component-cultibox Priority-Low Type-Enhancement | ```
Quelle est la procédure pour reproduire le problème?
1.
2.
3.
...
Quel est le résultat attendu? Qu'avez vous à la place?
Quelle version du logiciel / Cultibox utilisez-vous?
Sur quel système d'exploitation?
Indiquez les informations supplémentaires ci-dessous:
```
Original issue reported on code.google.com ... | 1.0 | [culti] ecran principal : affichagesymbol lune - ```
Quelle est la procédure pour reproduire le problème?
1.
2.
3.
...
Quel est le résultat attendu? Qu'avez vous à la place?
Quelle version du logiciel / Cultibox utilisez-vous?
Sur quel système d'exploitation?
Indiquez les informations supplémentaires ci-dessous:
... | non_secu | ecran principal affichagesymbol lune quelle est la procédure pour reproduire le problème quel est le résultat attendu qu avez vous à la place quelle version du logiciel cultibox utilisez vous sur quel système d exploitation indiquez les informations supplémentaires ci dessous ... | 0 |
254,971 | 21,891,772,621 | IssuesEvent | 2022-05-20 03:00:59 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Despesas com diárias - Despesas com diárias - Siplanweb - Santana do Garambéu | generalization test development template-Siplanweb tag-Despesas com diárias subtag-Despesas com diárias | DoD: Realizar o teste de Generalização do validador da tag Despesas com diárias - Despesas com diárias - Siplanweb para o Município de Santana do Garambéu. | 1.0 | Teste de generalizacao para a tag Despesas com diárias - Despesas com diárias - Siplanweb - Santana do Garambéu - DoD: Realizar o teste de Generalização do validador da tag Despesas com diárias - Despesas com diárias - Siplanweb para o Município de Santana do Garambéu. | non_secu | teste de generalizacao para a tag despesas com diárias despesas com diárias siplanweb santana do garambéu dod realizar o teste de generalização do validador da tag despesas com diárias despesas com diárias siplanweb para o município de santana do garambéu | 0 |
136,960 | 18,751,519,790 | IssuesEvent | 2021-11-05 03:01:44 | Dima2022/Resiliency-Studio | https://api.github.com/repos/Dima2022/Resiliency-Studio | closed | CVE-2017-18640 (High) detected in snakeyaml-1.17.jar - autoclosed | security vulnerability | ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.17.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http:/... | True | CVE-2017-18640 (High) detected in snakeyaml-1.17.jar - autoclosed - ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.17.jar</b></p></summary>
<p>YAML 1.1 p... | secu | cve high detected in snakeyaml jar autoclosed cve high severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file resiliency studio resiliency studio service pom xml path to vulnerable li... | 1 |
55,623 | 13,647,598,294 | IssuesEvent | 2020-09-26 04:15:41 | TerryCavanagh/diceydungeonsbeta | https://api.github.com/repos/TerryCavanagh/diceydungeonsbeta | closed | Quitting should save battle progress rather than ejecting you to the overworld | v0.6: 28th June Build | This would make save-scumming much less easy | 1.0 | Quitting should save battle progress rather than ejecting you to the overworld - This would make save-scumming much less easy | non_secu | quitting should save battle progress rather than ejecting you to the overworld this would make save scumming much less easy | 0 |
436,330 | 12,550,346,967 | IssuesEvent | 2020-06-06 10:46:55 | googleapis/google-api-java-client-services | https://api.github.com/repos/googleapis/google-api-java-client-services | opened | Synthesis failed for dns | api: dns autosynth failure priority: p1 type: bug | Hello! Autosynth couldn't regenerate dns. :broken_heart:
Here's the output from running `synth.py`:
```
2020-06-06 03:46:46,815 autosynth [INFO] > logs will be written to: /tmpfs/src/github/synthtool/logs/googleapis/google-api-java-client-services
2020-06-06 03:46:47,790 autosynth [DEBUG] > Running: git config --glob... | 1.0 | Synthesis failed for dns - Hello! Autosynth couldn't regenerate dns. :broken_heart:
Here's the output from running `synth.py`:
```
2020-06-06 03:46:46,815 autosynth [INFO] > logs will be written to: /tmpfs/src/github/synthtool/logs/googleapis/google-api-java-client-services
2020-06-06 03:46:47,790 autosynth [DEBUG] >... | non_secu | synthesis failed for dns hello autosynth couldn t regenerate dns broken heart here s the output from running synth py autosynth logs will be written to tmpfs src github synthtool logs googleapis google api java client services autosynth running git config global c... | 0 |
247,119 | 7,902,207,299 | IssuesEvent | 2018-07-01 00:13:27 | hack4impact-uiuc/h4i-recruitment | https://api.github.com/repos/hack4impact-uiuc/h4i-recruitment | closed | Split Express `app` configuration and server entrypoint into a separate file different from the routes | Priority: Critical help wanted | define api routes and middleware. This includes cors, bodyParser, error Handling, mongoose connections and server initialization. | 1.0 | Split Express `app` configuration and server entrypoint into a separate file different from the routes - define api routes and middleware. This includes cors, bodyParser, error Handling, mongoose connections and server initialization. | non_secu | split express app configuration and server entrypoint into a separate file different from the routes define api routes and middleware this includes cors bodyparser error handling mongoose connections and server initialization | 0 |
106,317 | 16,673,292,793 | IssuesEvent | 2021-06-07 13:32:02 | VivekBuzruk/Hygieia | https://api.github.com/repos/VivekBuzruk/Hygieia | closed | CVE-2020-5529 (High) detected in htmlunit-2.21.jar - autoclosed | security vulnerability | ## CVE-2020-5529 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>htmlunit-2.21.jar</b></p></summary>
<p>A headless browser intended for use in testing web-based applications.</p>
<p>Li... | True | CVE-2020-5529 (High) detected in htmlunit-2.21.jar - autoclosed - ## CVE-2020-5529 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>htmlunit-2.21.jar</b></p></summary>
<p>A headless bro... | secu | cve high detected in htmlunit jar autoclosed cve high severity vulnerability vulnerable library htmlunit jar a headless browser intended for use in testing web based applications library home page a href path to dependency file hygieia ui tests pom xml path to vulnerab... | 1 |
762,315 | 26,714,600,783 | IssuesEvent | 2023-01-28 10:27:30 | kubernetes/ingress-nginx | https://api.github.com/repos/kubernetes/ingress-nginx | closed | electionId configmap not getting deleted after uninstall | kind/support kind/bug priority/backlog lifecycle/rotten triage/accepted | **NGINX Ingress controller version** (exec into the pod and run nginx-ingress-controller --version.):
Using 4.0.13 helm chart
https://github.com/kubernetes/ingress-nginx/releases/download/helm-chart-4.0.13/ingress-nginx-4.0.13.tgz
**Kubernetes version** (use `kubectl version`):
k8s 1.22
**What happened**:
T... | 1.0 | electionId configmap not getting deleted after uninstall - **NGINX Ingress controller version** (exec into the pod and run nginx-ingress-controller --version.):
Using 4.0.13 helm chart
https://github.com/kubernetes/ingress-nginx/releases/download/helm-chart-4.0.13/ingress-nginx-4.0.13.tgz
**Kubernetes version** ... | non_secu | electionid configmap not getting deleted after uninstall nginx ingress controller version exec into the pod and run nginx ingress controller version using helm chart kubernetes version use kubectl version what happened the electionid configmap is not getting deleted a... | 0 |
26,159 | 4,593,647,577 | IssuesEvent | 2016-09-21 02:13:44 | afisher1/GridLAB-D | https://api.github.com/repos/afisher1/GridLAB-D | closed | #98 Meter not accruing power on energy,
| defect | The powerflow meter is not properly accumulating the power into the energy property. Power is being recorded, but is simply not being accumulated into energy.
,
| 1.0 | #98 Meter not accruing power on energy,
- The powerflow meter is not properly accumulating the power into the energy property. Power is being recorded, but is simply not being accumulated into energy.
,
| non_secu | meter not accruing power on energy the powerflow meter is not properly accumulating the power into the energy property power is being recorded but is simply not being accumulated into energy | 0 |
133,361 | 18,297,204,803 | IssuesEvent | 2021-10-05 21:43:12 | ghc-dev/Steven-Martin | https://api.github.com/repos/ghc-dev/Steven-Martin | opened | CVE-2021-21295 (Medium) detected in netty-codec-http-4.1.39.Final.jar | security vulnerability | ## CVE-2021-21295 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.39.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application fra... | True | CVE-2021-21295 (Medium) detected in netty-codec-http-4.1.39.Final.jar - ## CVE-2021-21295 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.39.Final.jar</b></p></su... | secu | cve medium detected in netty codec http final jar cve medium severity vulnerability vulnerable library netty codec http final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and ... | 1 |
32,277 | 12,102,268,027 | IssuesEvent | 2020-04-20 16:25:31 | Hyraze/infiniteglug | https://api.github.com/repos/Hyraze/infiniteglug | opened | CVE-2019-11358 (Medium) detected in jquery-2.1.4.min.js | security vulnerability | ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="ht... | True | CVE-2019-11358 (Medium) detected in jquery-2.1.4.min.js - ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript librar... | secu | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file tmp ws scm infiniteglug node modules js attic test moment index html path... | 1 |
18,338 | 10,928,339,726 | IssuesEvent | 2019-11-22 18:48:10 | Azure/azure-sdk-for-java | https://api.github.com/repos/Azure/azure-sdk-for-java | closed | [QUESTION] Azure Cosmos: ChangeFeedProcessor clarifications | Cosmos Question Service Attention customer-reported | **Query/Question**
I was interested in using the **[ChangeFeedProcessor](https://azure.github.io/azure-sdk-for-java/track1reports/com/azure/data/cosmos/ChangeFeedProcessor.html)** in order to get updates about upserts happening for a specific partition within a collection, but couldn't find any option to specify the... | 1.0 | [QUESTION] Azure Cosmos: ChangeFeedProcessor clarifications - **Query/Question**
I was interested in using the **[ChangeFeedProcessor](https://azure.github.io/azure-sdk-for-java/track1reports/com/azure/data/cosmos/ChangeFeedProcessor.html)** in order to get updates about upserts happening for a specific partition wi... | non_secu | azure cosmos changefeedprocessor clarifications query question i was interested in using the in order to get updates about upserts happening for a specific partition within a collection but couldn t find any option to specify the preferred partition furthermore i have some more doubts about changef... | 0 |
8,630 | 23,151,826,060 | IssuesEvent | 2022-07-29 09:04:31 | owncloud/android | https://api.github.com/repos/owncloud/android | opened | [BUG] [New arch] Crash when removing account | Crash New architecture |
### Steps to reproduce
1. Add account
2. Go to `Manage Accounts` and remove the account
### Actual behaviour
App crashes
### Expected behaviour
No crash
Can this problem be reproduced with the official owncloud server?
(url: https://demo.owncloud.org, user: test, password: test)
### Environmen... | 1.0 | [BUG] [New arch] Crash when removing account -
### Steps to reproduce
1. Add account
2. Go to `Manage Accounts` and remove the account
### Actual behaviour
App crashes
### Expected behaviour
No crash
Can this problem be reproduced with the official owncloud server?
(url: https://demo.owncloud.org, ... | non_secu | crash when removing account steps to reproduce add account go to manage accounts and remove the account actual behaviour app crashes expected behaviour no crash can this problem be reproduced with the official owncloud server url user test password test e... | 0 |
197,832 | 22,606,301,005 | IssuesEvent | 2022-06-29 13:32:18 | elikkatzgit/TestingPOM | https://api.github.com/repos/elikkatzgit/TestingPOM | closed | CVE-2020-24616 (High) detected in jackson-databind-2.7.2.jar - autoclosed | security vulnerability | ## CVE-2020-24616 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.7.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2020-24616 (High) detected in jackson-databind-2.7.2.jar - autoclosed - ## CVE-2020-24616 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.7.2.jar</b></p></summary... | secu | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href dependency hierarchy x jackson d... | 1 |
130,240 | 5,112,424,165 | IssuesEvent | 2017-01-06 11:07:59 | graphcool/console | https://api.github.com/repos/graphcool/console | reopened | Implement delete Permission | enhancement priority/high | Permissions kind of live it's own life atm.
I have a Post model which had `createNode` for authenticated users, i then added a new field `published: Boolean`, and then couldn't create a new post.
I looked in the `permission` tab in console and `createNode` had disappeared from the Post section.
I added it ag... | 1.0 | Implement delete Permission - Permissions kind of live it's own life atm.
I have a Post model which had `createNode` for authenticated users, i then added a new field `published: Boolean`, and then couldn't create a new post.
I looked in the `permission` tab in console and `createNode` had disappeared from the... | non_secu | implement delete permission permissions kind of live it s own life atm i have a post model which had createnode for authenticated users i then added a new field published boolean and then couldn t create a new post i looked in the permission tab in console and createnode had disappeared from the... | 0 |
30,663 | 11,842,017,212 | IssuesEvent | 2020-03-23 22:01:41 | Mohib-hub/karate | https://api.github.com/repos/Mohib-hub/karate | opened | CVE-2018-12023 (High) detected in jackson-databind-2.8.5.jar, jackson-databind-2.8.8.jar | security vulnerability | ## CVE-2018-12023 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.8.5.jar</b>, <b>jackson-databind-2.8.8.jar</b></p></summary>
<p>
<details><summary><b>jackson-dat... | True | CVE-2018-12023 (High) detected in jackson-databind-2.8.5.jar, jackson-databind-2.8.8.jar - ## CVE-2018-12023 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.8.5.jar... | secu | cve high detected in jackson databind jar jackson databind jar cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streami... | 1 |
19,509 | 10,361,352,217 | IssuesEvent | 2019-09-06 09:49:04 | hisptz/hris-maintenance-app | https://api.github.com/repos/hisptz/hris-maintenance-app | opened | CVE-2018-11695 (High) detected in opennms-opennms-source-23.0.0-1 | security vulnerability | ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-23.0.0-1</b></p></summary>
<p>
<p>A Java based fault and performance management system</p>
<p>Li... | True | CVE-2018-11695 (High) detected in opennms-opennms-source-23.0.0-1 - ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-23.0.0-1</b></p></summary>
<p... | secu | cve high detected in opennms opennms source cve high severity vulnerability vulnerable library opennmsopennms source a java based fault and performance management system library home page a href found in head commit a href library source files ... | 1 |
272,269 | 29,795,000,493 | IssuesEvent | 2023-06-16 01:03:12 | billmcchesney1/singleton | https://api.github.com/repos/billmcchesney1/singleton | closed | CVE-2021-28170 (Medium) detected in jakarta.el-3.0.3.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2021-28170 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jakarta.el-3.0.3.jar</b></p></summary>
<p>Jakarta Expression Language provides a specification document, API, refere... | True | CVE-2021-28170 (Medium) detected in jakarta.el-3.0.3.jar - autoclosed - ## CVE-2021-28170 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jakarta.el-3.0.3.jar</b></p></summary>
<p>Ja... | secu | cve medium detected in jakarta el jar autoclosed cve medium severity vulnerability vulnerable library jakarta el jar jakarta expression language provides a specification document api reference implementation and tck that describes an expression language for java app... | 1 |
249,576 | 26,954,448,650 | IssuesEvent | 2023-02-08 14:02:01 | simplycubed/terraform-google-static-assets | https://api.github.com/repos/simplycubed/terraform-google-static-assets | closed | CVE-2021-44716 (High) detected in github.com/docker/distribution-v2.8.1+incompatible - autoclosed | security vulnerability | ## CVE-2021-44716 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/docker/distribution-v2.8.1+incompatible</b></p></summary>
<p></p>
<p>Library home page: <a href="https://pr... | True | CVE-2021-44716 (High) detected in github.com/docker/distribution-v2.8.1+incompatible - autoclosed - ## CVE-2021-44716 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/docker/d... | secu | cve high detected in github com docker distribution incompatible autoclosed cve high severity vulnerability vulnerable library github com docker distribution incompatible library home page a href dependency hierarchy github com gruntwork io terratest roo... | 1 |
133,168 | 18,279,928,596 | IssuesEvent | 2021-10-05 00:59:18 | ghc-dev/Catherine-Hood | https://api.github.com/repos/ghc-dev/Catherine-Hood | opened | CVE-2020-9488 (Low) detected in log4j-core-2.8.2.jar | security vulnerability | ## CVE-2020-9488 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://log... | True | CVE-2020-9488 (Low) detected in log4j-core-2.8.2.jar - ## CVE-2020-9488 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p></summary>
<p>The Apache Log4j Implem... | secu | cve low detected in core jar cve low severity vulnerability vulnerable library core jar the apache implementation library home page a href path to dependency file catherine hood pom xml path to vulnerable library sitory org apache logging core core ... | 1 |
192,745 | 15,357,854,739 | IssuesEvent | 2021-03-01 14:10:37 | deepnight/gameBase | https://api.github.com/repos/deepnight/gameBase | closed | Add comments and doc | documentation | - [ ] move LEd doc generator to `deepnightLibs`
- [ ] add comments in Master branch
- [ ] update Advanced branch
- [ ] Publish doc somewhere | 1.0 | Add comments and doc - - [ ] move LEd doc generator to `deepnightLibs`
- [ ] add comments in Master branch
- [ ] update Advanced branch
- [ ] Publish doc somewhere | non_secu | add comments and doc move led doc generator to deepnightlibs add comments in master branch update advanced branch publish doc somewhere | 0 |
12,342 | 7,808,120,428 | IssuesEvent | 2018-06-11 19:06:28 | culturagovbr/mapasculturais | https://api.github.com/repos/culturagovbr/mapasculturais | closed | Correções gerais | bug enhancement usabilidade | - [x] Editar cor cinza para cor editável na barra de filtros de Editais
- [x] Rolagem de ano durante o tipo data no formulário dinâmico
- [x] Ao clicar no tipo/area de atuação de uma entidade na visualização no mapa, ou em lista, deverá ser filtrado pelo que foi clicado | True | Correções gerais - - [x] Editar cor cinza para cor editável na barra de filtros de Editais
- [x] Rolagem de ano durante o tipo data no formulário dinâmico
- [x] Ao clicar no tipo/area de atuação de uma entidade na visualização no mapa, ou em lista, deverá ser filtrado pelo que foi clicado | non_secu | correções gerais editar cor cinza para cor editável na barra de filtros de editais rolagem de ano durante o tipo data no formulário dinâmico ao clicar no tipo area de atuação de uma entidade na visualização no mapa ou em lista deverá ser filtrado pelo que foi clicado | 0 |
383,113 | 26,533,020,434 | IssuesEvent | 2023-01-19 13:52:22 | digital-asset/daml | https://api.github.com/repos/digital-asset/daml | opened | Document interfaces on the Ledger API | component/documentation roadmap/interfaces | Building on the example from https://github.com/digital-asset/daml/pull/15837, perhaps under https://docs.daml.com/app-dev/ledger-api.html, we should explain how interfaces can be used through the Ledger API (subscriptions/filters/exercise) | 1.0 | Document interfaces on the Ledger API - Building on the example from https://github.com/digital-asset/daml/pull/15837, perhaps under https://docs.daml.com/app-dev/ledger-api.html, we should explain how interfaces can be used through the Ledger API (subscriptions/filters/exercise) | non_secu | document interfaces on the ledger api building on the example from perhaps under we should explain how interfaces can be used through the ledger api subscriptions filters exercise | 0 |
52,066 | 13,722,079,492 | IssuesEvent | 2020-10-03 01:38:03 | sosaheri/github-actions-for-ci | https://api.github.com/repos/sosaheri/github-actions-for-ci | opened | CVE-2020-7608 (Medium) detected in yargs-parser-13.1.1.tgz, yargs-parser-11.1.1.tgz | security vulnerability | ## CVE-2020-7608 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>yargs-parser-13.1.1.tgz</b>, <b>yargs-parser-11.1.1.tgz</b></p></summary>
<p>
<details><summary><b>yargs-parser-13.... | True | CVE-2020-7608 (Medium) detected in yargs-parser-13.1.1.tgz, yargs-parser-11.1.1.tgz - ## CVE-2020-7608 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>yargs-parser-13.1.1.tgz</b>, <... | secu | cve medium detected in yargs parser tgz yargs parser tgz cve medium severity vulnerability vulnerable libraries yargs parser tgz yargs parser tgz yargs parser tgz the mighty option parser used by yargs library home page a href path to depen... | 1 |
84,212 | 15,720,859,889 | IssuesEvent | 2021-03-29 01:26:16 | greenetx/jenkins2-course-spring-boot | https://api.github.com/repos/greenetx/jenkins2-course-spring-boot | opened | CVE-2021-21346 (High) detected in xstream-1.4.7.jar | security vulnerability | ## CVE-2021-21346 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.7.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Pa... | True | CVE-2021-21346 (High) detected in xstream-1.4.7.jar - ## CVE-2021-21346 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.7.jar</b></p></summary>
<p>XStream is a serializatio... | secu | cve high detected in xstream jar cve high severity vulnerability vulnerable library xstream jar xstream is a serialization library from java objects to xml and back path to dependency file course spring boot spring boot autoconfigure pom xml path to vulnerable library ... | 1 |
48,689 | 13,392,376,687 | IssuesEvent | 2020-09-03 01:11:00 | LevyForchh/juice-shop | https://api.github.com/repos/LevyForchh/juice-shop | opened | CVE-2020-7720 (High) detected in node-forge-0.9.0.tgz | security vulnerability | ## CVE-2020-7720 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.9.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI,... | True | CVE-2020-7720 (High) detected in node-forge-0.9.0.tgz - ## CVE-2020-7720 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.9.0.tgz</b></p></summary>
<p>JavaScript implementa... | secu | cve high detected in node forge tgz cve high severity vulnerability vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file ... | 1 |
328,111 | 24,170,695,279 | IssuesEvent | 2022-09-22 18:55:52 | dafny-lang/dafny | https://api.github.com/repos/dafny-lang/dafny | opened | Distinguish good Dafny examples from regression tests | part: documentation kind: tests area: new users | There are a lot of excellent examples of small Dafny programs in the regression suite under `Test`. However, the regression suite's primary goal is good testing coverage for the set of all possible Dafny programs, not just well-written ones. By design we will need to include code we wouldn't recommend anyone write curr... | 1.0 | Distinguish good Dafny examples from regression tests - There are a lot of excellent examples of small Dafny programs in the regression suite under `Test`. However, the regression suite's primary goal is good testing coverage for the set of all possible Dafny programs, not just well-written ones. By design we will need... | non_secu | distinguish good dafny examples from regression tests there are a lot of excellent examples of small dafny programs in the regression suite under test however the regression suite s primary goal is good testing coverage for the set of all possible dafny programs not just well written ones by design we will need... | 0 |
289,344 | 31,932,891,749 | IssuesEvent | 2023-09-19 08:37:18 | Trinadh465/linux-4.1.15_CVE-2023-4128 | https://api.github.com/repos/Trinadh465/linux-4.1.15_CVE-2023-4128 | opened | CVE-2018-20669 (High) detected in multiple libraries | Mend: dependency security vulnerability | ## CVE-2018-20669 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.6</b>, <b>linux-stable-rtv4.1.33</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b></p></summary>
<p>
<... | True | CVE-2018-20669 (High) detected in multiple libraries - ## CVE-2018-20669 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.6</b>, <b>linux-stable-rtv4.1.33</b>, <b>linuxlin... | secu | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries linuxlinux linux stable linuxlinux linuxlinux vulnerability details an issue where a provided address with access ok is not checked was discovered i... | 1 |
273,803 | 29,831,092,479 | IssuesEvent | 2023-06-18 09:30:40 | RG4421/ampere-centos-kernel | https://api.github.com/repos/RG4421/ampere-centos-kernel | closed | CVE-2019-19072 (Medium) detected in linuxv5.2 - autoclosed | Mend: dependency security vulnerability | ## CVE-2019-19072 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/tor... | True | CVE-2019-19072 (Medium) detected in linuxv5.2 - autoclosed - ## CVE-2019-19072 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source ... | secu | cve medium detected in autoclosed cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in base branch amp centos kernel vulnerable source files kernel trace trace events filter c ... | 1 |
34,135 | 12,244,921,535 | IssuesEvent | 2020-05-05 12:04:44 | Souparnee/WebGoat2_20022020 | https://api.github.com/repos/Souparnee/WebGoat2_20022020 | opened | CVE-2018-11697 (High) detected in multiple libraries | security vulnerability | ## CVE-2018-11697 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.11.0.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.11.0.tgz</b></p></summary>
<p>Wrapper a... | True | CVE-2018-11697 (High) detected in multiple libraries - ## CVE-2018-11697 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.11.0.tgz</b></p></summary>
<p>
<details><summary>... | secu | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm docs package json path to vulnerable library tmp... | 1 |
186,259 | 21,920,125,620 | IssuesEvent | 2022-05-22 12:49:53 | turkdevops/elasticsearch | https://api.github.com/repos/turkdevops/elasticsearch | closed | CVE-2021-35517 (High) detected in commons-compress-1.5.jar - autoclosed | security vulnerability | ## CVE-2021-35517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-compress-1.5.jar</b></p></summary>
<p>Apache Commons Compress software defines an API for working with compres... | True | CVE-2021-35517 (High) detected in commons-compress-1.5.jar - autoclosed - ## CVE-2021-35517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-compress-1.5.jar</b></p></summary>
<... | secu | cve high detected in commons compress jar autoclosed cve high severity vulnerability vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip xz and ar cpio jar tar zip ... | 1 |
367,892 | 25,767,537,895 | IssuesEvent | 2022-12-09 04:01:48 | ccodwg/CovidTimelineCanada | https://api.github.com/repos/ccodwg/CovidTimelineCanada | closed | Explain `value` and `value_daily` in README | documentation | Clarify meanings for each dataset in the repository. | 1.0 | Explain `value` and `value_daily` in README - Clarify meanings for each dataset in the repository. | non_secu | explain value and value daily in readme clarify meanings for each dataset in the repository | 0 |
81,469 | 15,630,026,342 | IssuesEvent | 2021-03-22 01:07:33 | Palem1988/EIPs | https://api.github.com/repos/Palem1988/EIPs | opened | CVE-2018-17567 (High) detected in jekyll-3.6.2.gem | security vulnerability | ## CVE-2018-17567 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jekyll-3.6.2.gem</b></p></summary>
<p>Jekyll is a simple, blog aware, static site generator.</p>
<p>Library home page:... | True | CVE-2018-17567 (High) detected in jekyll-3.6.2.gem - ## CVE-2018-17567 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jekyll-3.6.2.gem</b></p></summary>
<p>Jekyll is a simple, blog aw... | secu | cve high detected in jekyll gem cve high severity vulnerability vulnerable library jekyll gem jekyll is a simple blog aware static site generator library home page a href path to dependency file eips gemfile lock path to vulnerable library var lib gems cac... | 1 |
108,496 | 16,777,922,889 | IssuesEvent | 2021-06-15 01:19:49 | renfei/GitPub | https://api.github.com/repos/renfei/GitPub | opened | CVE-2019-16943 (High) detected in jackson-databind-2.9.2.jar | security vulnerability | ## CVE-2019-16943 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-16943 (High) detected in jackson-databind-2.9.2.jar - ## CVE-2019-16943 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General... | secu | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file gitpub pom xml path to vulne... | 1 |
112,998 | 17,115,606,197 | IssuesEvent | 2021-07-11 09:29:06 | theHinneh/ridge-condos | https://api.github.com/repos/theHinneh/ridge-condos | opened | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz | security vulnerability | ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p... | True | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz - ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic... | secu | cve high detected in glob parent tgz cve high severity vulnerability vulnerable library glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file ridge condos package json path to vulnerable l... | 1 |
184,724 | 21,784,958,904 | IssuesEvent | 2022-05-14 01:57:31 | howlr-me/howlr-front | https://api.github.com/repos/howlr-me/howlr-front | closed | CVE-2019-10746 (High) detected in mixin-deep-1.3.2.tgz - autoclosed | security vulnerability | ## CVE-2019-10746 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mixin-deep-1.3.2.tgz</b></p></summary>
<p>Deeply mix the properties of objects into the first object. Like merge-deep,... | True | CVE-2019-10746 (High) detected in mixin-deep-1.3.2.tgz - autoclosed - ## CVE-2019-10746 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mixin-deep-1.3.2.tgz</b></p></summary>
<p>Deeply... | secu | cve high detected in mixin deep tgz autoclosed cve high severity vulnerability vulnerable library mixin deep tgz deeply mix the properties of objects into the first object like merge deep but doesn t clone library home page a href path to dependency file howlr fro... | 1 |
146,025 | 19,393,783,864 | IssuesEvent | 2021-12-18 01:03:32 | samqws-marketing/box_mojito | https://api.github.com/repos/samqws-marketing/box_mojito | closed | WS-2021-0491 (Medium) detected in logback-classic-1.2.3.jar - autoclosed | security vulnerability | ## WS-2021-0491 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>logback-classic-1.2.3.jar</b></p></summary>
<p>logback-classic module</p>
<p>Library home page: <a href="http://logbac... | True | WS-2021-0491 (Medium) detected in logback-classic-1.2.3.jar - autoclosed - ## WS-2021-0491 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>logback-classic-1.2.3.jar</b></p></summary>
... | secu | ws medium detected in logback classic jar autoclosed ws medium severity vulnerability vulnerable library logback classic jar logback classic module library home page a href path to dependency file box mojito test common pom xml path to vulnerable library home wss ... | 1 |
115,398 | 9,793,488,291 | IssuesEvent | 2019-06-10 20:05:18 | saltstack/salt | https://api.github.com/repos/saltstack/salt | closed | integration.states.test_pip_state.PipStateTest.test_issue_2028_pip_installed_state | Blocker Test Failure develop | ```
integration.states.test_pip_state.PipStateTest.test_issue_2028_pip_installed_state
--------------------------------------------------------------------------------
develop failed salt-fedora-28-py3
--------------------------------------------------------------------------------
False is not True. Salt Commen... | 1.0 | integration.states.test_pip_state.PipStateTest.test_issue_2028_pip_installed_state - ```
integration.states.test_pip_state.PipStateTest.test_issue_2028_pip_installed_state
--------------------------------------------------------------------------------
develop failed salt-fedora-28-py3
-----------------------------... | non_secu | integration states test pip state pipstatetest test issue pip installed state integration states test pip state pipstatetest test issue pip installed state develop failed salt fedora ... | 0 |
157,573 | 19,959,067,666 | IssuesEvent | 2022-01-28 05:23:35 | JeffResc/Is.gd-Node.js | https://api.github.com/repos/JeffResc/Is.gd-Node.js | closed | CVE-2015-9251 (Medium) detected in jquery-1.7.2.min.js | security vulnerability | ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="htt... | True | CVE-2015-9251 (Medium) detected in jquery-1.7.2.min.js - ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library ... | secu | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file is gd node js node modules marked www demo html path to vulnerable library i... | 1 |
5,928 | 6,089,140,087 | IssuesEvent | 2017-06-19 03:18:06 | piwik/piwik | https://api.github.com/repos/piwik/piwik | closed | Iframe buster not implemented in reports | Bug c: Security | According to #2701 all export links should be stripped out of auth_token. This isn't a case for link allowing to download file with email report content:

Users concern is that e... | True | Iframe buster not implemented in reports - According to #2701 all export links should be stripped out of auth_token. This isn't a case for link allowing to download file with email report content:

| 1.0 | Structs view is not compact in the compact view - Pack 0.93 13/09
Structs view is not compact in the compact view. Spacious above and below the table
| non_secu | structs view is not compact in the compact view pack structs view is not compact in the compact view spacious above and below the table | 0 |
75,526 | 9,858,956,651 | IssuesEvent | 2019-06-20 08:28:02 | CriticalDevelopmentsInc/Bull3tLauncher | https://api.github.com/repos/CriticalDevelopmentsInc/Bull3tLauncher | opened | Documentation | documentation | ### Bullet Documentation
**Using The Login System**
When using the login system, you should be presented with:
- a Username Box
- a Password Box
- and a Serial Key Box
When Typing In This Information Your Should Always Keep a Note of Your Details As You Get The Chance Of It Being Shown Everytime You Login, Thanks... | 1.0 | Documentation - ### Bullet Documentation
**Using The Login System**
When using the login system, you should be presented with:
- a Username Box
- a Password Box
- and a Serial Key Box
When Typing In This Information Your Should Always Keep a Note of Your Details As You Get The Chance Of It Being Shown Everytime Y... | non_secu | documentation bullet documentation using the login system when using the login system you should be presented with a username box a password box and a serial key box when typing in this information your should always keep a note of your details as you get the chance of it being shown everytime y... | 0 |
173,939 | 6,534,638,623 | IssuesEvent | 2017-08-31 11:39:58 | quintel/etengine | https://api.github.com/repos/quintel/etengine | closed | Number of units of households_water_heater_network_gas is not set correctly | Bug High priority | Setting its share to 100%, set the number of units to zero!
@antw I realised that this technology is an exception as it is used to balance the group and has an empty update statement:
https://github.com/quintel/etsource/blob/master/inputs/demand/households/households_hot_water/households_water_heater_network_gas_... | 1.0 | Number of units of households_water_heater_network_gas is not set correctly - Setting its share to 100%, set the number of units to zero!
@antw I realised that this technology is an exception as it is used to balance the group and has an empty update statement:
https://github.com/quintel/etsource/blob/master/inpu... | non_secu | number of units of households water heater network gas is not set correctly setting its share to set the number of units to zero antw i realised that this technology is an exception as it is used to balance the group and has an empty update statement | 0 |
37,434 | 10,000,928,012 | IssuesEvent | 2019-07-12 14:29:41 | CircleCI-Public/circleci-cli | https://api.github.com/repos/CircleCI-Public/circleci-cli | closed | local execute - filenames with spaces cause code checkout to fail | Local Builds bug | - [x] I have read [Contribution Guidelines](https://github.com/CircleCI-Public/circleci-cli/blob/master/CONTRIBUTING.md).
- [x] I have checked for similar issues and haven't found anything relevant.
- [x] This is not a security issue (which should be reported here: https://circleci.com/security/)
**Do you want to ... | 1.0 | local execute - filenames with spaces cause code checkout to fail - - [x] I have read [Contribution Guidelines](https://github.com/CircleCI-Public/circleci-cli/blob/master/CONTRIBUTING.md).
- [x] I have checked for similar issues and haven't found anything relevant.
- [x] This is not a security issue (which should be... | non_secu | local execute filenames with spaces cause code checkout to fail i have read i have checked for similar issues and haven t found anything relevant this is not a security issue which should be reported here do you want to request a feature or report a bug bug what is the cur... | 0 |
362,033 | 25,358,382,281 | IssuesEvent | 2022-11-20 16:04:24 | pac1006/GESPRO_GESTIONTAREAS | https://api.github.com/repos/pac1006/GESPRO_GESTIONTAREAS | closed | Rematar memoria | documentation | - [ ] Enlace Google Play.
- [ ] Imagen CI
- [ ] Tabla de estadísticas
- [ ] Firmar electrónicamente
- [ ] Imagen página web o google play | 1.0 | Rematar memoria - - [ ] Enlace Google Play.
- [ ] Imagen CI
- [ ] Tabla de estadísticas
- [ ] Firmar electrónicamente
- [ ] Imagen página web o google play | non_secu | rematar memoria enlace google play imagen ci tabla de estadísticas firmar electrónicamente imagen página web o google play | 0 |
313,836 | 23,493,904,919 | IssuesEvent | 2022-08-17 21:52:08 | typescript-eslint/typescript-eslint | https://api.github.com/repos/typescript-eslint/typescript-eslint | opened | Docs: Clear policy for what would preclude a sponsor from being featured on the website | documentation accepting prs | ### Before You File a Documentation Request Please Confirm You Have Done The Following...
- [X] I have looked for existing [open or closed documentation requests](https://github.com/typescript-eslint/typescript-eslint/issues?q=is%3Aissue+label%3Adocumentation) that match my proposal.
- [X] I have [read the FAQ](https:... | 1.0 | Docs: Clear policy for what would preclude a sponsor from being featured on the website - ### Before You File a Documentation Request Please Confirm You Have Done The Following...
- [X] I have looked for existing [open or closed documentation requests](https://github.com/typescript-eslint/typescript-eslint/issues?q=is... | non_secu | docs clear policy for what would preclude a sponsor from being featured on the website before you file a documentation request please confirm you have done the following i have looked for existing that match my proposal i have and my problem is not listed suggested changes ex... | 0 |
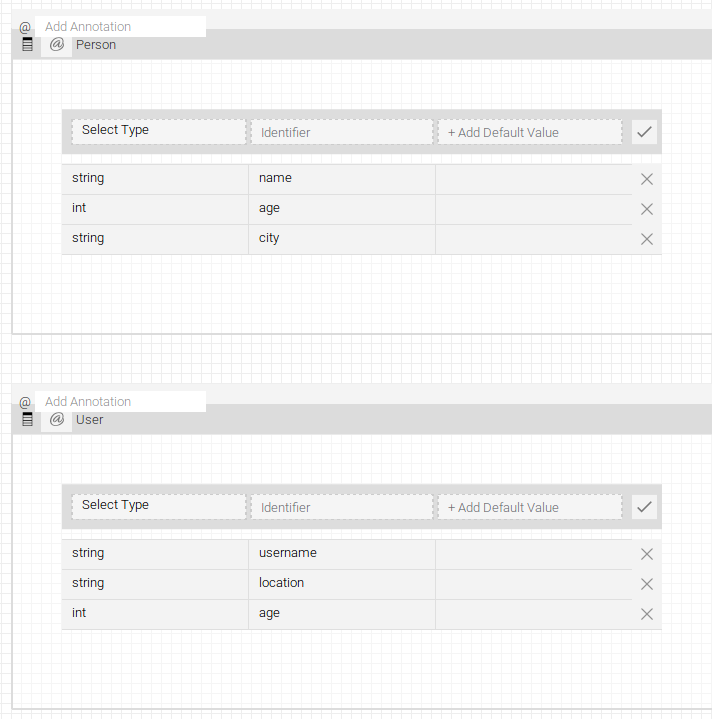
194,371 | 6,894,241,503 | IssuesEvent | 2017-11-23 09:15:12 | ballerinalang/composer | https://api.github.com/repos/ballerinalang/composer | closed | [Design view] Cannot make a function public, wrong syntax is given | 0.95.1 Priority/Highest Severity/Critical | As shown in the below image, when trying to make a function public by design view, it results in an error as the generated syntax is wrong.
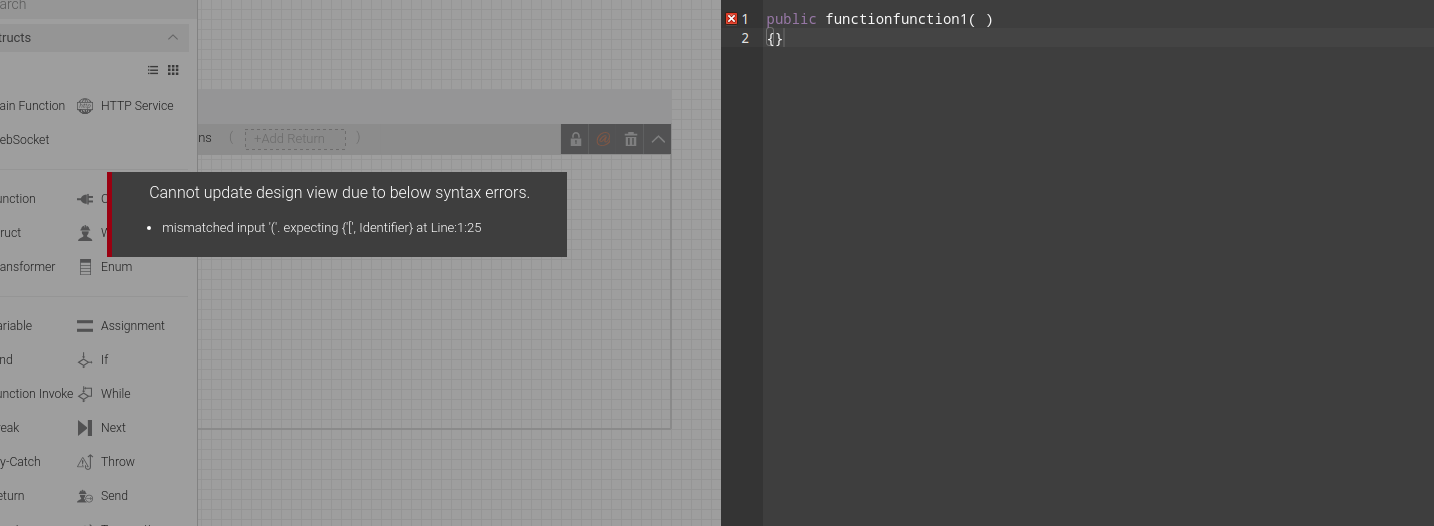
| 1.0 | [Design view] Cannot make a function public, wrong syntax is given - As shown in the below image, when trying to make a function public by design view, it results in an error as the generated syntax is wrong.
 - a security-behavior tool added and currently developed in Knative. This tool is also applicable for more generic Kubernetes web service use cases and may later be extended for additional Kubernetes use cases.
Security Guard starts with the assumption... | True | REQUEST: Request a Learning session - Security-Guard - [knative.dev/security-guard](http://knative.dev/security-guard) - a security-behavior tool added and currently developed in Knative. This tool is also applicable for more generic Kubernetes web service use cases and may later be extended for additional Kubernetes ... | secu | request request a learning session security guard a security behavior tool added and currently developed in knative this tool is also applicable for more generic kubernetes web service use cases and may later be extended for additional kubernetes use cases security guard starts with the assumption that... | 1 |
140,960 | 11,385,196,219 | IssuesEvent | 2020-01-29 10:35:41 | akasolace/HO | https://api.github.com/repos/akasolace/HO | reopened | Out Of Bounds Exception for Hall of Fame players | status: needs test | Version 2.0
If I try to select an Hall of Fame players into Player Analysis (F5 menu), I got an error
```
java.lang.ArrayIndexOutOfBoundsException: -1
at core.gui.model.UserColumnFactory$6.getTableEntry(UserColumnFactory.java:148)
at core.gui.model.PlayerAnalysisModel.initData(PlayerAnalysisModel.java:134)
a... | 1.0 | Out Of Bounds Exception for Hall of Fame players - Version 2.0
If I try to select an Hall of Fame players into Player Analysis (F5 menu), I got an error
```
java.lang.ArrayIndexOutOfBoundsException: -1
at core.gui.model.UserColumnFactory$6.getTableEntry(UserColumnFactory.java:148)
at core.gui.model.PlayerAnaly... | non_secu | out of bounds exception for hall of fame players version if i try to select an hall of fame players into player analysis menu i got an error java lang arrayindexoutofboundsexception at core gui model usercolumnfactory gettableentry usercolumnfactory java at core gui model playeranalysis... | 0 |
12,830 | 15,094,635,325 | IssuesEvent | 2021-02-07 07:25:20 | vesoft-inc/nebula-graph | https://api.github.com/repos/vesoft-inc/nebula-graph | closed | [openCypher tck case] invalid integer error check | bug incompatible |
```
(czp@nebula) [nba]> yield 9223372#54775808 AS literal
+---------+
| 9223372 |
+---------+
| 9223372 |
+---------+
Got 1 rows (time spent 19652/29050 us)
``` | True | [openCypher tck case] invalid integer error check -
```
(czp@nebula) [nba]> yield 9223372#54775808 AS literal
+---------+
| 9223372 |
+---------+
| 9223372 |
+---------+
Got 1 rows (time spent 19652/29050 us)
``` | non_secu | invalid integer error check czp nebula yield as literal got rows time spent us | 0 |
199,834 | 22,715,354,124 | IssuesEvent | 2022-07-06 01:07:47 | nexmo-community/santa-tracker-sms | https://api.github.com/repos/nexmo-community/santa-tracker-sms | opened | spring-boot-starter-data-jpa-2.1.0.RELEASE.jar: 5 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-starter-data-jpa-2.1.0.RELEASE.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanne... | True | spring-boot-starter-data-jpa-2.1.0.RELEASE.jar: 5 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-starter-data-jpa-2.1.0.RELEASE.jar</b></p></summary>
<p></p... | secu | spring boot starter data jpa release jar vulnerabilities highest severity is vulnerable library spring boot starter data jpa release jar path to dependency file build gradle path to vulnerable library home wss scanner gradle caches modules files org ... | 1 |
71,724 | 15,207,911,959 | IssuesEvent | 2021-02-17 01:18:58 | billmcchesney1/hadoop | https://api.github.com/repos/billmcchesney1/hadoop | opened | CVE-2020-7598 (Medium) detected in minimist-0.0.10.tgz, minimist-0.0.8.tgz | security vulnerability | ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.10.tgz</b>, <b>minimist-0.0.8.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.10.tgz</b></... | True | CVE-2020-7598 (Medium) detected in minimist-0.0.10.tgz, minimist-0.0.8.tgz - ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.10.tgz</b>, <b>minimist-0.... | secu | cve medium detected in minimist tgz minimist tgz cve medium severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file hadoop hadoop yarn proje... | 1 |
250,176 | 7,969,962,866 | IssuesEvent | 2018-07-16 10:59:30 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | m.facebook.com - site is not usable | browser-firefox-mobile priority-critical | <!-- @browser: Firefox Mobile 63.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.0.0; Mobile; rv:63.0) Gecko/63.0 Firefox/63.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://m.facebook.com/
**Browser / Version**: Firefox Mobile 63.0
**Operating System**: Android 8.0.0
**Tested Another Browser**: No
**Pr... | 1.0 | m.facebook.com - site is not usable - <!-- @browser: Firefox Mobile 63.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.0.0; Mobile; rv:63.0) Gecko/63.0 Firefox/63.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://m.facebook.com/
**Browser / Version**: Firefox Mobile 63.0
**Operating System**: Android 8.0.... | non_secu | m facebook com site is not usable url browser version firefox mobile operating system android tested another browser no problem type site is not usable description can t paste my password i use a randomly generated password that is difficult to type steps to ... | 0 |
181,247 | 14,011,901,657 | IssuesEvent | 2020-10-29 08:13:06 | microsoft/STL | https://api.github.com/repos/microsoft/STL | closed | tr1 tests are misusing initializer_list | test work in progress | `initializer_list` does not have a constructor that takes a pair of pointers - it is implementation detail.
Occurrences are in tr1 tests. Search for `initializer_list` and inspect each use.
`initializer_list` should probably be kept for cases where it is created from an array created by `initializer_list`, just s... | 1.0 | tr1 tests are misusing initializer_list - `initializer_list` does not have a constructor that takes a pair of pointers - it is implementation detail.
Occurrences are in tr1 tests. Search for `initializer_list` and inspect each use.
`initializer_list` should probably be kept for cases where it is created from an a... | non_secu | tests are misusing initializer list initializer list does not have a constructor that takes a pair of pointers it is implementation detail occurrences are in tests search for initializer list and inspect each use initializer list should probably be kept for cases where it is created from an array... | 0 |
57,279 | 24,082,573,979 | IssuesEvent | 2022-09-19 08:04:17 | Azure/azure-cli | https://api.github.com/repos/Azure/azure-cli | closed | `lab vm create` fails with error that gives no information. | Service Attention DevTestLabs |
---
I've run the following command and it gives me no information:
```
> az lab vm create --lab-name wilxlab --name wilxlabvm0 -g wilxgroup --image "Ubuntu Server 16.04 LTS" --image-type gallery
Admin Password:
Confirm Admin Password:
Deployment failed. Correlation ID: 67e36dbf-5dbc-4819-bd9f-2624b2b23bbc. An e... | 1.0 | `lab vm create` fails with error that gives no information. -
---
I've run the following command and it gives me no information:
```
> az lab vm create --lab-name wilxlab --name wilxlabvm0 -g wilxgroup --image "Ubuntu Server 16.04 LTS" --image-type gallery
Admin Password:
Confirm Admin Password:
Deployment fail... | non_secu | lab vm create fails with error that gives no information i ve run the following command and it gives me no information az lab vm create lab name wilxlab name g wilxgroup image ubuntu server lts image type gallery admin password confirm admin password deployment failed correla... | 0 |
151,508 | 13,424,997,105 | IssuesEvent | 2020-09-06 08:14:53 | FOAP-NETMIND-PROMOCIO-2020/friendlyrent | https://api.github.com/repos/FOAP-NETMIND-PROMOCIO-2020/friendlyrent | closed | Documentar esquema de la aplicación | documentation | 1. Identificar todas las partes de la aplicación Web distribuida; y como se comunican las partes entre sí. Realizar un esquema parecido a los que aparecen en [estas imágenes.](https://www.google.com/search?q=nodejs+architecture+mongodb&safe=off&sxsrf=ALeKk03EFNtJ6Bf5961DJS1Hlo_7DMsVRg:1597244748038&source=lnms&tbm=isch... | 1.0 | Documentar esquema de la aplicación - 1. Identificar todas las partes de la aplicación Web distribuida; y como se comunican las partes entre sí. Realizar un esquema parecido a los que aparecen en [estas imágenes.](https://www.google.com/search?q=nodejs+architecture+mongodb&safe=off&sxsrf=ALeKk03EFNtJ6Bf5961DJS1Hlo_7DMs... | non_secu | documentar esquema de la aplicación identificar todas las partes de la aplicación web distribuida y como se comunican las partes entre sí realizar un esquema parecido a los que aparecen en deberáían relacionarse los siguientes conceptos que papel tiene nodejs express en la arquitectura important... | 0 |
108,513 | 16,777,928,219 | IssuesEvent | 2021-06-15 01:20:35 | renfei/GitPub | https://api.github.com/repos/renfei/GitPub | opened | CVE-2020-9548 (High) detected in jackson-databind-2.9.2.jar | security vulnerability | ## CVE-2020-9548 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming... | True | CVE-2020-9548 (High) detected in jackson-databind-2.9.2.jar - ## CVE-2020-9548 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General d... | secu | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file gitpub pom xml path to vulne... | 1 |
47,294 | 5,874,320,104 | IssuesEvent | 2017-05-15 15:48:08 | zmap/zcrypto | https://api.github.com/repos/zmap/zcrypto | opened | Add tests for x509/cert_pool.go | good-first-bug tests | CertPool currently has no tests. We've added some functionality to it, so we should definitely test that. Current versions of the Golang stdlib might have added tests for cert_pool that we could use as a basis.
The new functions as of May 15, 2017 are:
- CertPool.Certificates()
- CertPool.Contains()
- CertPool.Su... | 1.0 | Add tests for x509/cert_pool.go - CertPool currently has no tests. We've added some functionality to it, so we should definitely test that. Current versions of the Golang stdlib might have added tests for cert_pool that we could use as a basis.
The new functions as of May 15, 2017 are:
- CertPool.Certificates()
- ... | non_secu | add tests for cert pool go certpool currently has no tests we ve added some functionality to it so we should definitely test that current versions of the golang stdlib might have added tests for cert pool that we could use as a basis the new functions as of may are certpool certificates certpoo... | 0 |
43,716 | 23,345,260,687 | IssuesEvent | 2022-08-09 17:19:36 | ZacharyFolk/simplefolk | https://api.github.com/repos/ZacharyFolk/simplefolk | closed | Remove Guttenberg CSS | performance | Disable the core WordPress loading of /wp-includes/css/dist/block-library/style.min.css
note: the theme will not work with Guttenberg after this | True | Remove Guttenberg CSS - Disable the core WordPress loading of /wp-includes/css/dist/block-library/style.min.css
note: the theme will not work with Guttenberg after this | non_secu | remove guttenberg css disable the core wordpress loading of wp includes css dist block library style min css note the theme will not work with guttenberg after this | 0 |
32,265 | 12,102,203,756 | IssuesEvent | 2020-04-20 16:19:30 | AOSC-Dev/aosc-os-abbs | https://api.github.com/repos/AOSC-Dev/aosc-os-abbs | closed | Chromium: security update to 79.0.3945.79 | security to-stable upgrade | **CVE IDs:** [CVE-2019-13725, CVE-2019-13726, CVE-2019-13727, CVE-2019-13728, CVE-2019-13729, CVE-2019-13730, CVE-2019-13732, CVE-2019-13734, CVE-2019-13735, CVE-2019-13764, CVE-2019-13736, CVE-2019-13737, CVE-2019-13738, CVE-2019-13739, CVE-2019-13740, CVE-2019-13741, CVE-2019-13742, CVE-2019-13743, CVE-2019-13744, CV... | True | Chromium: security update to 79.0.3945.79 - **CVE IDs:** [CVE-2019-13725, CVE-2019-13726, CVE-2019-13727, CVE-2019-13728, CVE-2019-13729, CVE-2019-13730, CVE-2019-13732, CVE-2019-13734, CVE-2019-13735, CVE-2019-13764, CVE-2019-13736, CVE-2019-13737, CVE-2019-13738, CVE-2019-13739, CVE-2019-13740, CVE-2019-13741, CVE-20... | secu | chromium security update to cve ids other security advisory ids n a descriptions too long didn t copy see link above patches n a poc s n a architectural progress | 1 |
165,559 | 6,278,191,204 | IssuesEvent | 2017-07-18 13:55:21 | our-city-app/oca-backend | https://api.github.com/repos/our-city-app/oca-backend | closed | Changing contact and setting PO number of free orders/charges | priority_major state_inprogress type_feature | In the past it was possible to set the PO number or to change the contact of orders. However, since everything is free, orders are immediately signed and it has become impossible to do this. | 1.0 | Changing contact and setting PO number of free orders/charges - In the past it was possible to set the PO number or to change the contact of orders. However, since everything is free, orders are immediately signed and it has become impossible to do this. | non_secu | changing contact and setting po number of free orders charges in the past it was possible to set the po number or to change the contact of orders however since everything is free orders are immediately signed and it has become impossible to do this | 0 |
171,369 | 13,229,952,009 | IssuesEvent | 2020-08-18 09:01:46 | gambitph/Stackable | https://api.github.com/repos/gambitph/Stackable | closed | Some blocks encountered an error when you add them in the block editor | [block] feature [block] pricing box [block] team member [block] testimonial bug critical | Even if you didn't change or edit anything, some blocks will error out just by adding them to the block editor.
I'm using the **Version 2.9.0-responsive-fix-v3 plugin**.
These are the ... | 1.0 | Some blocks encountered an error when you add them in the block editor - Even if you didn't change or edit anything, some blocks will error out just by adding them to the block editor.
I'... | non_secu | some blocks encountered an error when you add them in the block editor even if you didn t change or edit anything some blocks will error out just by adding them to the block editor i m using the version responsive fix plugin these are the blocks that error out by adding them in the block... | 0 |
34,754 | 12,294,735,347 | IssuesEvent | 2020-05-11 01:21:05 | doc-ai/react-native-animatable | https://api.github.com/repos/doc-ai/react-native-animatable | opened | WS-2020-0070 (High) detected in lodash-3.10.1.tgz | security vulnerability | ## WS-2020-0070 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="... | True | WS-2020-0070 (High) detected in lodash-3.10.1.tgz - ## WS-2020-0070 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash mo... | secu | ws high detected in lodash tgz ws high severity vulnerability vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file react native animatable examples makeitrain package json path to vulnerable libr... | 1 |
109,774 | 11,648,664,652 | IssuesEvent | 2020-03-01 22:02:34 | Chilacoders/Chilacoders | https://api.github.com/repos/Chilacoders/Chilacoders | closed | Comentarios de su documentación | documentation good first issue | Hola @chilacoders, el planteamiento de su objetivo general y específico está bien pero les pido mejorar su redacción, comparto los puntos en los que se pueden basar.
Su objetivo general debe reflejar la esencia del planteamiento del problema y la idea expresada, respondiendo las preguntas: ¿Qué? ¿Cómo? ¿Para qué?
... | 1.0 | Comentarios de su documentación - Hola @chilacoders, el planteamiento de su objetivo general y específico está bien pero les pido mejorar su redacción, comparto los puntos en los que se pueden basar.
Su objetivo general debe reflejar la esencia del planteamiento del problema y la idea expresada, respondiendo las pr... | non_secu | comentarios de su documentación hola chilacoders el planteamiento de su objetivo general y específico está bien pero les pido mejorar su redacción comparto los puntos en los que se pueden basar su objetivo general debe reflejar la esencia del planteamiento del problema y la idea expresada respondiendo las pr... | 0 |
87,751 | 15,790,301,220 | IssuesEvent | 2021-04-02 01:04:22 | Farsene1/Object-Oriented-Programming-Project | https://api.github.com/repos/Farsene1/Object-Oriented-Programming-Project | opened | CVE-2019-0221 (Medium) detected in tomcat-embed-core-8.5.34.jar | security vulnerability | ## CVE-2019-0221 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.34.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https... | True | CVE-2019-0221 (Medium) detected in tomcat-embed-core-8.5.34.jar - ## CVE-2019-0221 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.34.jar</b></p></summary>
<p>C... | secu | cve medium detected in tomcat embed core jar cve medium severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file object oriented programming project client pom xml path to vulnerabl... | 1 |
15,683 | 2,868,984,898 | IssuesEvent | 2015-06-05 22:22:49 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | support or complain if `pub run my_bin_script` depends on dev-dependencies | Area-Pub Priority-Unassigned Pub-Run Triaged Type-Defect | This feature request summarizes a discussion Natalie, Kevin, and I had last week.
Most people are surprised if in package `a` you do:
pub run foo
and it works, but when running it in package `b`, as:
pub run a:foo
it fails.
This typically happens if `foo` uses code from `dev_dependencies... | 1.0 | support or complain if `pub run my_bin_script` depends on dev-dependencies - This feature request summarizes a discussion Natalie, Kevin, and I had last week.
Most people are surprised if in package `a` you do:
pub run foo
and it works, but when running it in package `b`, as:
pub run a:foo
... | non_secu | support or complain if pub run my bin script depends on dev dependencies this feature request summarizes a discussion natalie kevin and i had last week most people are surprised if in package a you do nbsp nbsp pub run foo and it works but when running it in package b as nbsp nbsp pub run a foo ... | 0 |
129,693 | 18,107,487,194 | IssuesEvent | 2021-09-22 20:56:07 | Tim-Demo/JS-Demo | https://api.github.com/repos/Tim-Demo/JS-Demo | opened | CVE-2020-7608 (Medium) detected in yargs-parser-2.4.1.tgz | security vulnerability | ## CVE-2020-7608 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>yargs-parser-2.4.1.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href=... | True | CVE-2020-7608 (Medium) detected in yargs-parser-2.4.1.tgz - ## CVE-2020-7608 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>yargs-parser-2.4.1.tgz</b></p></summary>
<p>the mighty op... | secu | cve medium detected in yargs parser tgz cve medium severity vulnerability vulnerable library yargs parser tgz the mighty option parser used by yargs library home page a href path to dependency file js demo package json path to vulnerable library js demo node modules ... | 1 |
800,049 | 28,323,852,405 | IssuesEvent | 2023-04-11 05:06:33 | FTC7393/FtcRobotController | https://api.github.com/repos/FTC7393/FtcRobotController | closed | Fetcher stops too suddenly when joystick released | bug Teleop Extremely high priority | The naive algorithm to capture the encoder value when the joystick is released results in a non-intuitive overshoot and back-up jerking motion. The solution is to tell it to stop moving again when its velocity is near zero, so that it slows down quickly but doesn't back up.
We tried this today using the motor's get... | 1.0 | Fetcher stops too suddenly when joystick released - The naive algorithm to capture the encoder value when the joystick is released results in a non-intuitive overshoot and back-up jerking motion. The solution is to tell it to stop moving again when its velocity is near zero, so that it slows down quickly but doesn't b... | non_secu | fetcher stops too suddenly when joystick released the naive algorithm to capture the encoder value when the joystick is released results in a non intuitive overshoot and back up jerking motion the solution is to tell it to stop moving again when its velocity is near zero so that it slows down quickly but doesn t b... | 0 |
118,057 | 17,576,346,602 | IssuesEvent | 2021-08-15 17:31:26 | turkdevops/brackets | https://api.github.com/repos/turkdevops/brackets | reopened | CVE-2021-23343 (High) detected in path-parse-1.0.6.tgz | security vulnerability | ## CVE-2021-23343 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p></summary>
<p>Node.js path.parse() ponyfill</p>
<p>Library home page: <a href="https://reg... | True | CVE-2021-23343 (High) detected in path-parse-1.0.6.tgz - ## CVE-2021-23343 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p></summary>
<p>Node.js path.parse(... | secu | cve high detected in path parse tgz cve high severity vulnerability vulnerable library path parse tgz node js path parse ponyfill library home page a href path to dependency file brackets package json path to vulnerable library brackets node modules npm node module... | 1 |
75,977 | 14,544,782,167 | IssuesEvent | 2020-12-15 18:40:47 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | ICE: exhaustiveness-non-exhaustive.rs with -Zinstrument-coverage: sumup_counter_operand should have a value | A-code-coverage C-bug I-ICE T-compiler glacier requires-nightly | <!--
Thank you for finding an Internal Compiler Error! 🧊 If possible, try to provide
a minimal verifiable example. You can read "Rust Bug Minimization Patterns" for
how to create smaller examples.
http://blog.pnkfx.org/blog/2019/11/18/rust-bug-minimization-patterns/
-->
### Code
code from `./src/test/ui/... | 1.0 | ICE: exhaustiveness-non-exhaustive.rs with -Zinstrument-coverage: sumup_counter_operand should have a value - <!--
Thank you for finding an Internal Compiler Error! 🧊 If possible, try to provide
a minimal verifiable example. You can read "Rust Bug Minimization Patterns" for
how to create smaller examples.
http:... | non_secu | ice exhaustiveness non exhaustive rs with zinstrument coverage sumup counter operand should have a value thank you for finding an internal compiler error 🧊 if possible try to provide a minimal verifiable example you can read rust bug minimization patterns for how to create smaller examples ... | 0 |
679,358 | 23,229,702,823 | IssuesEvent | 2022-08-03 06:17:50 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Removing an NFT from a collection removes all NFTs of that collection | priority/P3 OS/Android OS/Desktop | If I go and try to remove one NFTs in a collection as other NFTs I have in the same collection, all remove from my portfolio. I guess we are probably removing by contract ID only and not taking into account the Token ID. | 1.0 | Removing an NFT from a collection removes all NFTs of that collection - If I go and try to remove one NFTs in a collection as other NFTs I have in the same collection, all remove from my portfolio. I guess we are probably removing by contract ID only and not taking into account the Token ID. | non_secu | removing an nft from a collection removes all nfts of that collection if i go and try to remove one nfts in a collection as other nfts i have in the same collection all remove from my portfolio i guess we are probably removing by contract id only and not taking into account the token id | 0 |
194,572 | 22,262,032,768 | IssuesEvent | 2022-06-10 02:00:48 | ShaikUsaf/linux-4.19.72_CVE-2020-10757 | https://api.github.com/repos/ShaikUsaf/linux-4.19.72_CVE-2020-10757 | reopened | CVE-2019-19332 (Medium) detected in linuxlinux-4.19.236 | security vulnerability | ## CVE-2019-19332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.236</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge... | True | CVE-2019-19332 (Medium) detected in linuxlinux-4.19.236 - ## CVE-2019-19332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.236</b></p></summary>
<p>
<p>The Linux Ker... | secu | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files ... | 1 |
301,184 | 22,739,643,124 | IssuesEvent | 2022-07-07 01:35:06 | nebari-dev/nebari | https://api.github.com/repos/nebari-dev/nebari | closed | [DOC] Tutorial on creating a new environment | area: documentation 📖 | How do I create a new environment on Nebari?
The conda-store UI is changing, so this may need to be on hold. Or should we go ahead with the current UI?
Maybe add a separate page for defining environments as part of the repo/IaC?
Include information on how to install something with pip (with warning signs, etc)... | 1.0 | [DOC] Tutorial on creating a new environment - How do I create a new environment on Nebari?
The conda-store UI is changing, so this may need to be on hold. Or should we go ahead with the current UI?
Maybe add a separate page for defining environments as part of the repo/IaC?
Include information on how to insta... | non_secu | tutorial on creating a new environment how do i create a new environment on nebari the conda store ui is changing so this may need to be on hold or should we go ahead with the current ui maybe add a separate page for defining environments as part of the repo iac include information on how to install s... | 0 |
139,903 | 20,981,429,318 | IssuesEvent | 2022-03-28 20:21:42 | quantumlib/Cirq | https://api.github.com/repos/quantumlib/Cirq | closed | setup a CHANGELOG.md | kind/health triage/accepted needs agreed design area/releases | It is fairly common to have a portable, human readable changelog for OSS projects. I think we should have one. For more background - I mostly agree with the reasons listed in https://keepachangelog.com/en/1.0.0/
My main motivation would be to introduce an "Unreleased" section, that would talk about Deprecations, Br... | 1.0 | setup a CHANGELOG.md - It is fairly common to have a portable, human readable changelog for OSS projects. I think we should have one. For more background - I mostly agree with the reasons listed in https://keepachangelog.com/en/1.0.0/
My main motivation would be to introduce an "Unreleased" section, that would talk... | non_secu | setup a changelog md it is fairly common to have a portable human readable changelog for oss projects i think we should have one for more background i mostly agree with the reasons listed in my main motivation would be to introduce an unreleased section that would talk about deprecations breaking chang... | 0 |
92,595 | 15,857,528,109 | IssuesEvent | 2021-04-08 05:00:50 | AOSC-Dev/aosc-os-abbs | https://api.github.com/repos/AOSC-Dev/aosc-os-abbs | closed | curl: security update to 7.76.0 | security upgrade | **CVE IDs:** CVE-2021-22876, CVE-2021-22890.
**Other security advisory IDs:** N/A
**Description:**
CVE-2021-22876:
```
libcurl does not strip off user credentials from the URL when automatically
populating the `Referer:` HTTP request header field in outgoing HTTP requests,
and therefore risks leaking sen... | True | curl: security update to 7.76.0 - **CVE IDs:** CVE-2021-22876, CVE-2021-22890.
**Other security advisory IDs:** N/A
**Description:**
CVE-2021-22876:
```
libcurl does not strip off user credentials from the URL when automatically
populating the `Referer:` HTTP request header field in outgoing HTTP requests... | secu | curl security update to cve ids cve cve other security advisory ids n a description cve libcurl does not strip off user credentials from the url when automatically populating the referer http request header field in outgoing http requests and therefore risks... | 1 |
166,858 | 20,725,601,988 | IssuesEvent | 2022-03-14 01:13:21 | jtimberlake/serverless-artillery | https://api.github.com/repos/jtimberlake/serverless-artillery | closed | CVE-2021-23566 (Medium) detected in nanoid-2.1.6.tgz - autoclosed | security vulnerability | ## CVE-2021-23566 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nanoid-2.1.6.tgz</b></p></summary>
<p>A tiny (139 bytes), secure URL-friendly unique string ID generator</p>
<p>Libr... | True | CVE-2021-23566 (Medium) detected in nanoid-2.1.6.tgz - autoclosed - ## CVE-2021-23566 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nanoid-2.1.6.tgz</b></p></summary>
<p>A tiny (13... | secu | cve medium detected in nanoid tgz autoclosed cve medium severity vulnerability vulnerable library nanoid tgz a tiny bytes secure url friendly unique string id generator library home page a href path to dependency file package json path to vulnerable library ... | 1 |
186,106 | 21,916,171,737 | IssuesEvent | 2022-05-21 21:28:33 | turkdevops/vuepress-next | https://api.github.com/repos/turkdevops/vuepress-next | closed | CVE-2022-0686 (High) detected in url-parse-1.5.3.tgz - autoclosed | security vulnerability | ## CVE-2022-0686 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser en... | True | CVE-2022-0686 (High) detected in url-parse-1.5.3.tgz - autoclosed - ## CVE-2022-0686 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p></summary>
<p>Small foot... | secu | cve high detected in url parse tgz autoclosed cve high severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file package json pat... | 1 |
708,469 | 24,342,589,202 | IssuesEvent | 2022-10-01 22:26:27 | kubernetes/ingress-nginx | https://api.github.com/repos/kubernetes/ingress-nginx | closed | Request update to authentication proxy example | kind/feature lifecycle/rotten needs-triage needs-priority | Regarding page:
https://kubernetes.github.io/ingress-nginx/examples/auth/oauth-external-auth/
I'd update it myself but haven't yet reached success implementing it.
| 1.0 | Request update to authentication proxy example - Regarding page:
https://kubernetes.github.io/ingress-nginx/examples/auth/oauth-external-auth/
I'd update it myself but haven't yet reached success implementing it.
| non_secu | request update to authentication proxy example regarding page i d update it myself but haven t yet reached success implementing it | 0 |
302,097 | 9,255,057,992 | IssuesEvent | 2019-03-16 05:43:57 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | opened | www.google.com - design is broken | browser-firefox-mobile browser-focus-geckoview priority-critical | <!-- @browser: Firefox Mobile 65.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.0.0; Mobile; rv:65.0) Gecko/65.0 Firefox/65.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https://www.google.com/?gws_rd=ssl
**Browser / Version**: Firefox Mobile 65.0
**Operating System**: Androi... | 1.0 | www.google.com - design is broken - <!-- @browser: Firefox Mobile 65.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.0.0; Mobile; rv:65.0) Gecko/65.0 Firefox/65.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https://www.google.com/?gws_rd=ssl
**Browser / Version**: Firefox Mobi... | non_secu | design is broken url browser version firefox mobile operating system android tested another browser yes problem type design is broken description it shows google s old design steps to reproduce browser configuration none from with ... | 0 |
376,875 | 11,157,530,068 | IssuesEvent | 2019-12-25 13:23:44 | Disfactory/Disfactory | https://api.github.com/repos/Disfactory/Disfactory | opened | 照片新增後端花太多時間 | Backend enhancement medium priority | **Describe the bug**
上傳照片有時候要花上快十秒
**To Reproduce**
上傳看看就知道了
**Expected behavior**
要再快一點
| 1.0 | 照片新增後端花太多時間 - **Describe the bug**
上傳照片有時候要花上快十秒
**To Reproduce**
上傳看看就知道了
**Expected behavior**
要再快一點
| non_secu | 照片新增後端花太多時間 describe the bug 上傳照片有時候要花上快十秒 to reproduce 上傳看看就知道了 expected behavior 要再快一點 | 0 |
526,306 | 15,286,029,077 | IssuesEvent | 2021-02-23 14:15:23 | Poobslag/turbofat | https://api.github.com/repos/Poobslag/turbofat | opened | Improve performance of rendering creature heads | priority-3 | Based on the performance investigation documented in #767, creature heads are potentially a performance bottleneck.
We could render these heads more efficiently, in a way that does not require 30 nodes per creature. At a minimum, we should at least prototype a creature with these improvements and see how what impact... | 1.0 | Improve performance of rendering creature heads - Based on the performance investigation documented in #767, creature heads are potentially a performance bottleneck.
We could render these heads more efficiently, in a way that does not require 30 nodes per creature. At a minimum, we should at least prototype a creatu... | non_secu | improve performance of rendering creature heads based on the performance investigation documented in creature heads are potentially a performance bottleneck we could render these heads more efficiently in a way that does not require nodes per creature at a minimum we should at least prototype a creature ... | 0 |
150,704 | 11,981,931,794 | IssuesEvent | 2020-04-07 12:04:31 | MicronOxford/cockpit | https://api.github.com/repos/MicronOxford/cockpit | closed | StageMover - do not move coarse Z at start of experiment | critical needs testing | Check that the requested range is addressable by the fine stage in the current position. If not, tell the user / ask them if we should move the coarse stage.
| 1.0 | StageMover - do not move coarse Z at start of experiment - Check that the requested range is addressable by the fine stage in the current position. If not, tell the user / ask them if we should move the coarse stage.
| non_secu | stagemover do not move coarse z at start of experiment check that the requested range is addressable by the fine stage in the current position if not tell the user ask them if we should move the coarse stage | 0 |
139,706 | 18,853,745,567 | IssuesEvent | 2021-11-12 01:38:42 | sesong11/example | https://api.github.com/repos/sesong11/example | opened | CVE-2020-10672 (High) detected in jackson-databind-2.9.9.jar | security vulnerability | ## CVE-2020-10672 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2020-10672 (High) detected in jackson-databind-2.9.9.jar - ## CVE-2020-10672 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General... | secu | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file example quartz jdbc pom xml ... | 1 |
127,946 | 5,040,847,879 | IssuesEvent | 2016-12-19 07:59:13 | Apollo-Community/ApolloStation | https://api.github.com/repos/Apollo-Community/ApolloStation | closed | Riot Suits now fit in bags. | easy to fix priority: low | As the title says. When inspected, it says that they are normal items, rather than the "bulky" ones they are. Should be a simple matter of changing the code back to bulky. | 1.0 | Riot Suits now fit in bags. - As the title says. When inspected, it says that they are normal items, rather than the "bulky" ones they are. Should be a simple matter of changing the code back to bulky. | non_secu | riot suits now fit in bags as the title says when inspected it says that they are normal items rather than the bulky ones they are should be a simple matter of changing the code back to bulky | 0 |
197,031 | 22,572,158,840 | IssuesEvent | 2022-06-28 02:00:42 | AlexRogalskiy/scala-patterns | https://api.github.com/repos/AlexRogalskiy/scala-patterns | opened | CVE-2021-42740 (High) detected in shell-quote-1.7.2.tgz | security vulnerability | ## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shell-quote-1.7.2.tgz</b></p></summary>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://r... | True | CVE-2021-42740 (High) detected in shell-quote-1.7.2.tgz - ## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shell-quote-1.7.2.tgz</b></p></summary>
<p>quote and parse s... | secu | cve high detected in shell quote tgz cve high severity vulnerability vulnerable library shell quote tgz quote and parse shell commands library home page a href path to dependency file tilt modules tilt inspector package json path to vulnerable library tilt modules ... | 1 |
255,984 | 19,349,425,105 | IssuesEvent | 2021-12-15 14:17:29 | Machine-Listeners-Valencia/DCASE2021-Task1b | https://api.github.com/repos/Machine-Listeners-Valencia/DCASE2021-Task1b | closed | pretrained vgg16 model | documentation | Hi !
Can you provide the hdf5 file of the pre-trained VGG16 model on places365 ?
### pre_model = load_model('PATH_TO\vgg16_places_t2_1x.hdf5', compile=False) ###
Thanks! | 1.0 | pretrained vgg16 model - Hi !
Can you provide the hdf5 file of the pre-trained VGG16 model on places365 ?
### pre_model = load_model('PATH_TO\vgg16_places_t2_1x.hdf5', compile=False) ###
Thanks! | non_secu | pretrained model hi can you provide the file of the pre trained model on pre model load model path to places compile false thanks | 0 |
45,279 | 18,523,662,312 | IssuesEvent | 2021-10-20 17:44:32 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | Allow setting Host Name in route53 healthcheck | enhancement service/route53 stale | <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not l... | 1.0 | Allow setting Host Name in route53 healthcheck - <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maint... | non_secu | allow setting host name in healthcheck community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help priorit... | 0 |
16,849 | 10,574,372,936 | IssuesEvent | 2019-10-07 13:53:36 | edgexfoundry/edgex-go | https://api.github.com/repos/edgexfoundry/edgex-go | closed | Implementation of Vault initialization& Unseal in the security-secretstore-setup | enhancement fuji security-services | to utilize Vault as a secret store for EdgeX, it is needed to initialize and unseal Vault in the project of security-secretstore-setup | 1.0 | Implementation of Vault initialization& Unseal in the security-secretstore-setup - to utilize Vault as a secret store for EdgeX, it is needed to initialize and unseal Vault in the project of security-secretstore-setup | non_secu | implementation of vault initialization unseal in the security secretstore setup to utilize vault as a secret store for edgex it is needed to initialize and unseal vault in the project of security secretstore setup | 0 |
413,804 | 27,970,106,084 | IssuesEvent | 2023-03-25 00:38:57 | ramidedantas/GCMS-2022-1 | https://api.github.com/repos/ramidedantas/GCMS-2022-1 | closed | Prática 1 - GitHub Issues - Instruções Gerais | documentation | **Bem-vindos ao repositório da disciplina.**
Sigam as instruções da prática com atenção. Para este passo, dê uma reação neste comentário e depois faça um novo comentário:
* Colocar *link* para um repositório seu (caso tenha);
* Caso não tenha, incluir link para o repositório que você explorou acima;
* Colocar ima... | 1.0 | Prática 1 - GitHub Issues - Instruções Gerais - **Bem-vindos ao repositório da disciplina.**
Sigam as instruções da prática com atenção. Para este passo, dê uma reação neste comentário e depois faça um novo comentário:
* Colocar *link* para um repositório seu (caso tenha);
* Caso não tenha, incluir link para o rep... | non_secu | prática github issues instruções gerais bem vindos ao repositório da disciplina sigam as instruções da prática com atenção para este passo dê uma reação neste comentário e depois faça um novo comentário colocar link para um repositório seu caso tenha caso não tenha incluir link para o rep... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.